Less Identity Chaos.
More Data Analytics.
Elimity Insights allows security and IAM teams to easily answer the ever-growing number of IAM data questions.
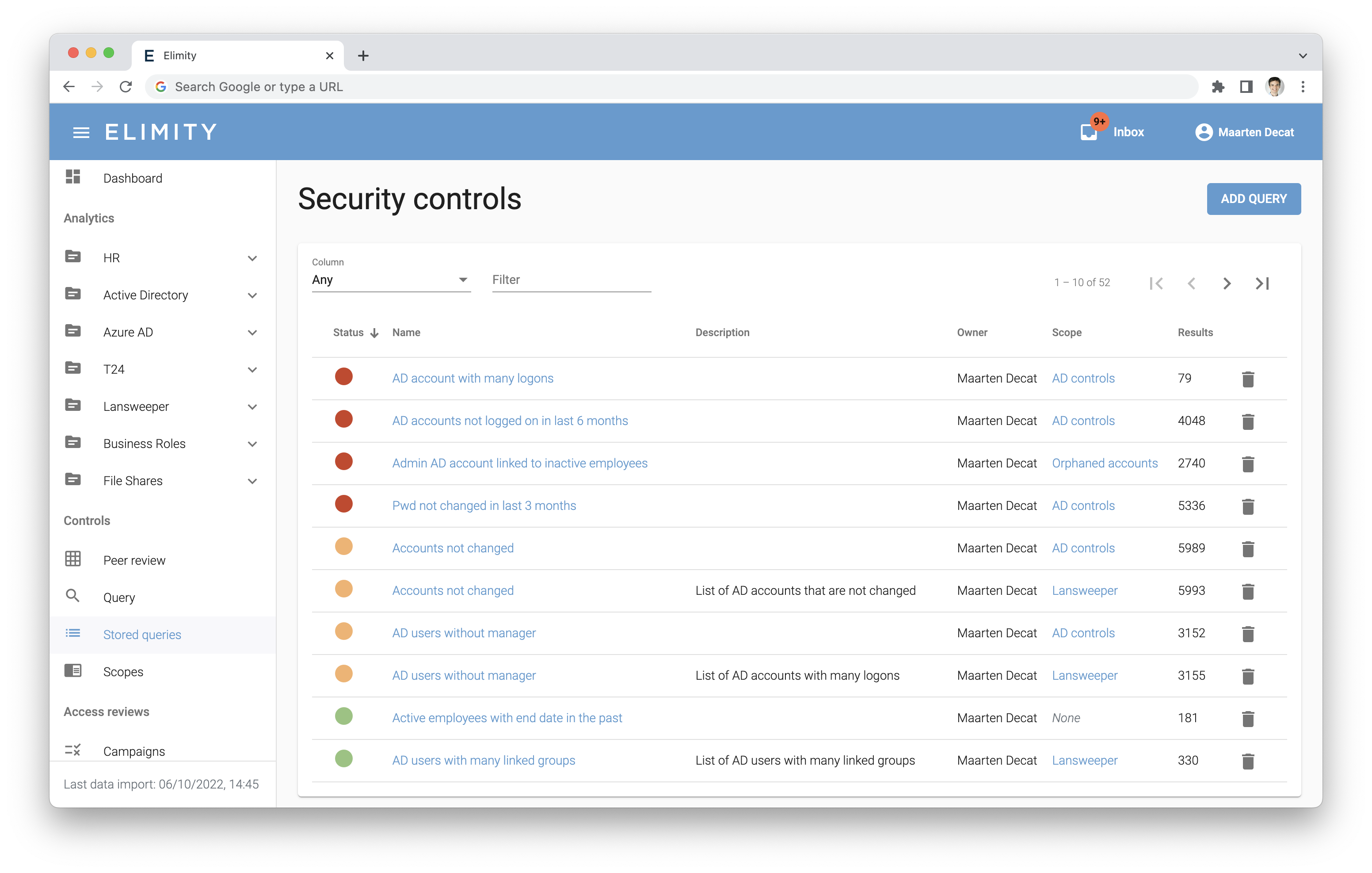
Easily understand who can currently access what, identify risks, act upon these and prove that you've taken action afterwards.
Can you answer these questions?
✅ Which contractor accounts have to be deleted?
Identity analytics helps you answer these questions and mitigate risks in a matter of days.
No matter your IAM maturity,
the Elimity platform helps you along
You have an IGA suite in place
Add Identity Analytics to your existing IGA, automate security controls and answer the day-to-day identity data queries.
You have an IGA suite partially deployed
Gain the needed identity data insights and cover the gaps prior to or during complex and lengthy IGA projects.
You require control of user access without costly IGA
Take control of users and their access to crucial applications with minimal effort.
ELIMITY INSIGHTS PLATFORM
Take control of User Access at speed
Understand your user access surface quickly and easily
Set up connectors to common applications such as Active Directory, Azure AD and Okta with just a few clicks. Connect to any other application without writing any line of code using our Integration Framework.
Achieve mature identity governance
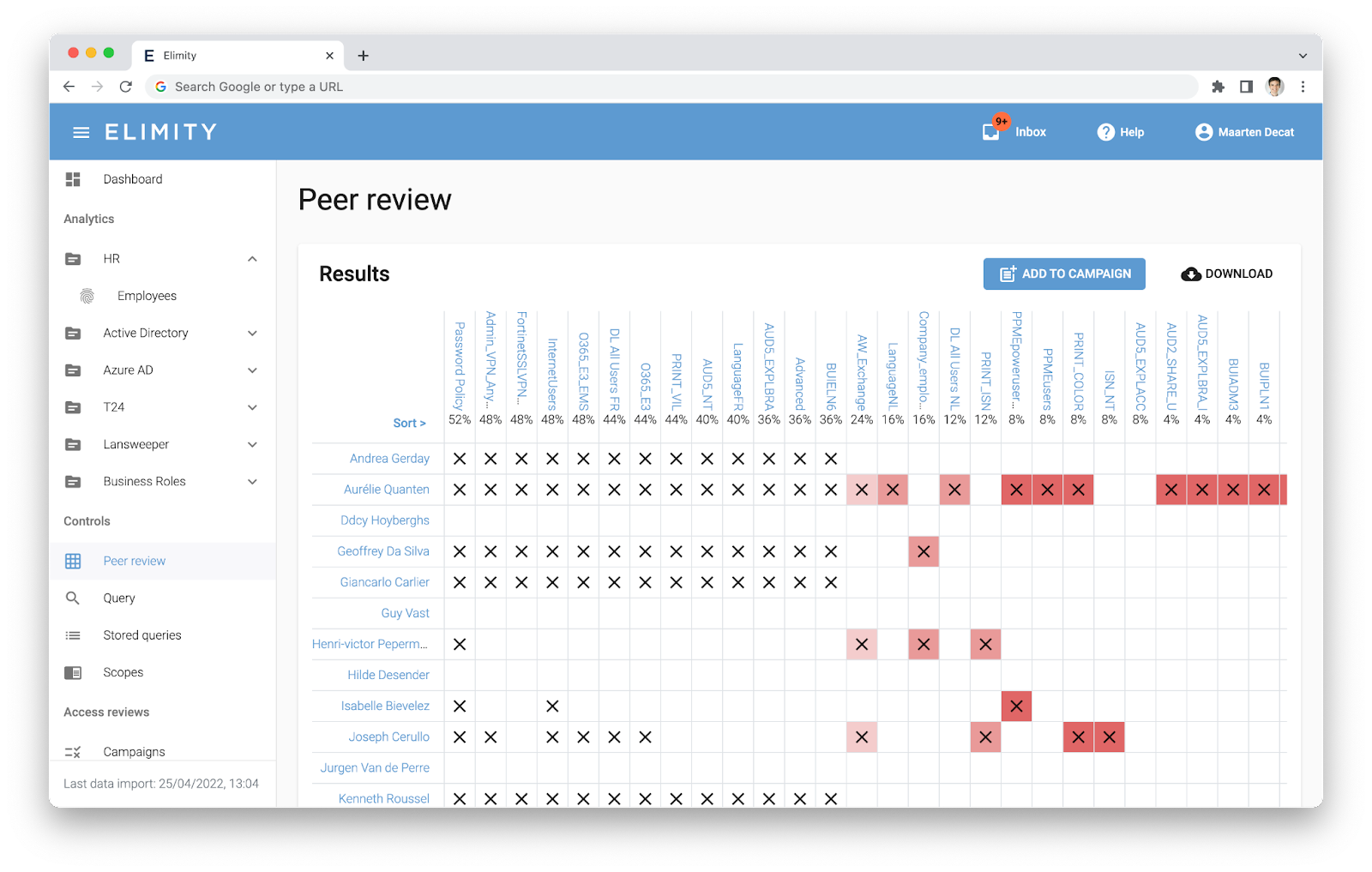
Consolidate control by easily implementing the needed identity governance processes. Send out access reviews to team leaders and application owners. Start creating roles based on the current permissions of your users. Integrate with ITSM to automatically implement the necessary changes.
What our customers say
“Elimity's platform provided crucial insights regarding the security of our IT assets. Even more important, it allowed us to share the responsibility of user access with the business units."

“Monitoring user access to our organisation’s data used to be done manually. Elimity’s platform automated this process, as well as reports on the risks and controls in place, saving our security team valuable time."

"As a vendor of software for financial organisations, we are obliged to report on the security of our IT assets and data. We leverage Elimity's reporting on user access in our RFPs, without requesting time from the security team."

3 Ways Identity Data Analytics Drives IAM Success.
Learn how the IAM team at a large financial institution decreased the time to generate IAM reports from 3 weeks to 2 minutes.
KPI-Driven approach to IAM
Our guide walks you through everything you need to start using KPIs to improve your IAM security.
Your Ultimate IGA-Deployment Checklist
Large organization speeds up and de-risks deployment of a new IGA suite
Get notified on new cyber insights and relevant updates
Be the first to know about new cyber trends and take your security expertise to the next level.





![[SMART MOCKUP] [GUIDES] [KPI GUIDE WITHOUT BACKGROUND]](https://elimity.com/hubfs/%5BSMART%20MOCKUP%5D%20%5BGUIDES%5D%20%5BKPI%20GUIDE%20WITHOUT%20BACKGROUND%5D.png)